The Ultimate Bug Bounty Notes Pack
If you're trying to break into bug bounty hunting or level up your current workflow, the hardest part usually isn’t motivation; it’s knowing what to study, what tools to use, and how to structure your process without wasting months jumping between scattered resources. This pack was built to remove that friction and give you a clear, practical path from beginner to confident hunter.
Inside The Ultimate Bug Bounty Notes Pack, you get four tightly connected resources that walk you through the full lifecycle of bug bounty hunting from understanding how to start, to running recon, using professional tools, and exploiting real-world web vulnerabilities.
What’s Inside the Pack
1 - Bug Bounty Getting Started Guide
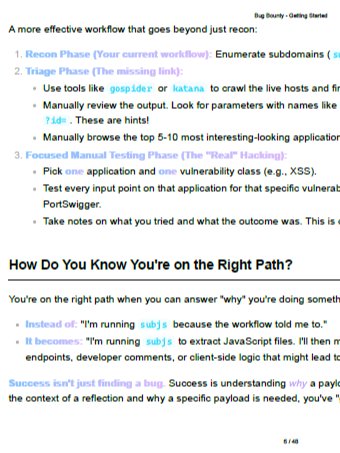
This is your entry point into the bug bounty world. It explains how to choose your first vulnerability, build repeatable workflows, and write professional bug reports that actually get accepted. It covers essentials like structured reporting, respecting program scope, demonstrating impact, and producing reproducible proof-of-concept evidence. You’ll also learn how to structure reports using standardized templates and how to think like a researcher rather than just running tools blindly.
2- Bug Bounty Recon & Exploitation Cheat Sheet
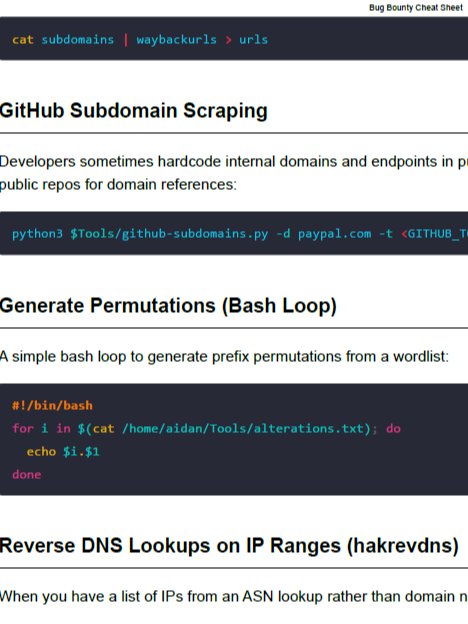
This is the methodology engine of the pack. It provides a structured, step-by-step recon workflow covering subdomain discovery, ASN reconnaissance, JavaScript analysis, content discovery, fingerprinting, and sensitive data hunting. Instead of guessing what to do next, you follow tested sequences used across real bug bounty engagements, including VPS-based recon workflows and automated enumeration strategies.
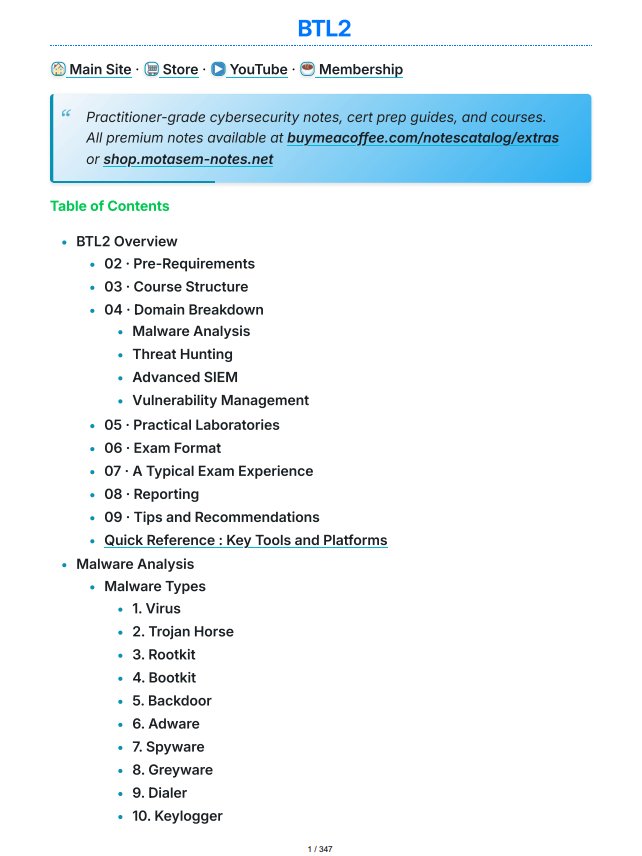
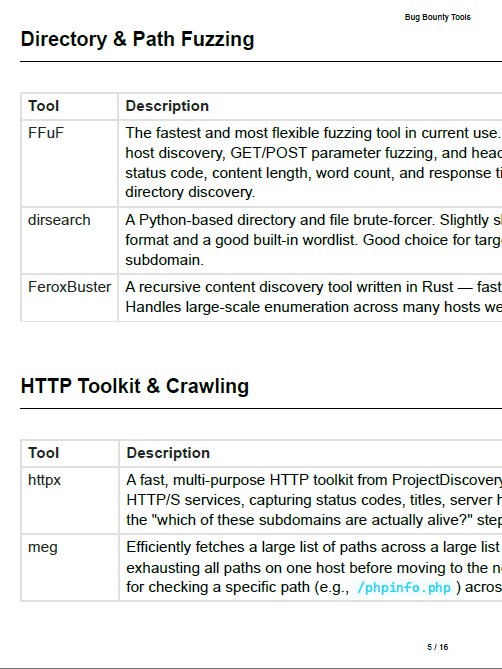
3 - Bug Bounty Tools Reference Guide
This section organizes the essential tools used in professional web testing and bug bounty hunting. It explains the purpose of each tool, where it fits in the workflow, and how it contributes to manual testing and traffic analysis. You’ll gain clarity on industry-standard tools such as web proxies, packet analyzers, and extension ecosystems that expand testing capabilities.
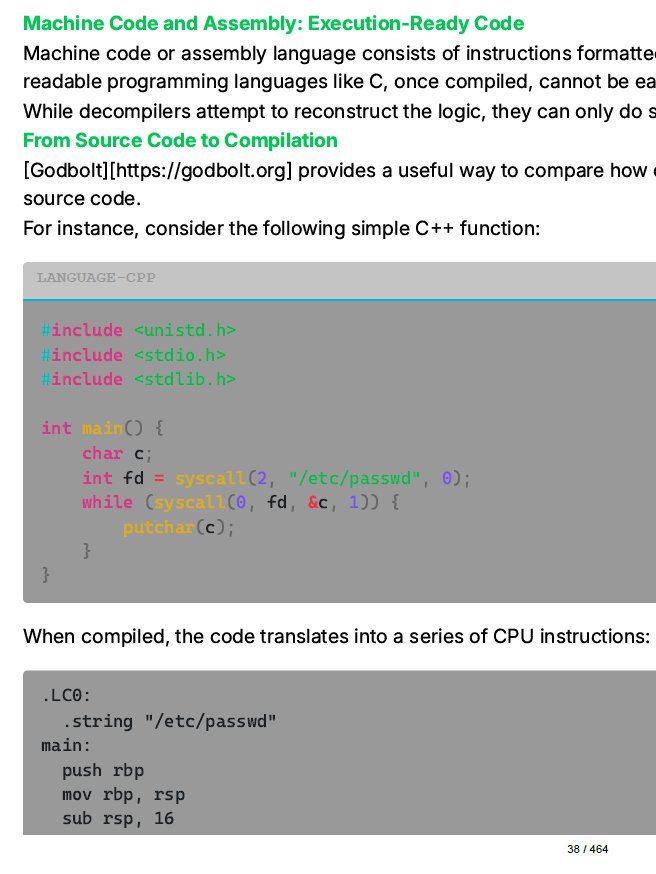
4 - Web Hacking & Penetration Testing Master Notes
This is the deep technical core of the pack. It contains extensive coverage of web technologies, HTTP communication, session handling, enumeration, and real-world attack techniques including SQL Injection, XSS, SSRF, file inclusion, authentication flaws, API vulnerabilities, and more. Rather than shallow summaries, this section provides practitioner-level explanations, attack workflows, and defensive insights that mirror real-world testing environments.
Who This Pack Is For
This pack is built for individuals who want structure instead of randomness.
It is especially valuable for:
- Beginners entering bug bounty hunting with no clear starting point
- Cybersecurity students preparing for web security careers
- Pentesting learners transitioning from theory to hands-on practice
- Developers and IT professionals wanting offensive security skills
- Intermediate hunters who need workflow clarity and better methodology
Anyone serious about finding vulnerabilities not just reading about them will benefit from having everything organized into a single coherent learning path.
What You’ll Learn and Be Able to Do
By working through this pack, you develop operational thinking not just technical knowledge.
You will:
- Understand how real bug bounty workflows are structured
- Build repeatable reconnaissance pipelines
- Use professional-grade tools with confidence
- Identify common and advanced web vulnerabilities
- Write clear, professional vulnerability reports
- Understand how web applications function internally
- Move from guessing to method-driven testing
- Reduce wasted time jumping between fragmented tutorials
The biggest advantage is momentum. Instead of spending months figuring out what to learn next, you move through a connected system that builds skill layer by layer.